The following table compares some of the biometric systems used lately, from the point of view of accuracy, cost, devices required and social acceptability.
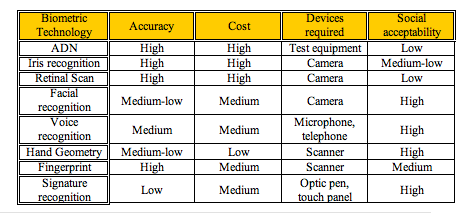

From this comparative table we can deduce that the most adequate methodology is the fingerprint authentication.
What are the goodness and weakness about the current technology?
Each one of the Technologies used in our days bring us a manner to restrict the access to a system, allowing the entrance only to those persons who know a specific code, own a card or have determined physic marks. The more complex is the system, the most difficult is to be attacked, although it will be more expensive and will require more software and hardware resources. When a new authentication system is implanted, it is essential a judgement between simplicity, price and efficiency, as well as social acceptability.
The password method is the cheapest and simplest technology, because it only requires elementary software resources.
On the other hand, this system is easily attackable, since he is quite simple to obtain the data from a person, either extracting the information to the person itself using deceits, or attacking the software of the system. For example, it can be easily installed in the computer, a program that simulates the “user name and password” window, so that when the user introduces his data in that window, that will be collected by the “Spy” program. Immediately after this, it appears the true window, identical, and the user will simply believe that he has been mistaken. So, this method, in spite of being usually used, for example, to access banking accounts, is not at all the most indicated if we want a safe system, and in a short-time future is tried to be changed by most immune methods.
The Smart Cards are very useful since they can be easily combined with other authentication systems, serving as storage system. Self-containment of smart card makes it resistant to attack as it does not need to depend upon potentially vulnerable external resources. But its small size and bend requirements (which are designed to protect the card physically), limits the memory and processing resources. And used like the only identification system, is not excessively trustworthy, since it can be easily stolen, lost or simply forgotten at home. Besides, sometimes they are combined with cryptography methods, which makes them more difficult (more expensive) to implement.
The Digital Signature is very difficult to falsify, since is encrypted by complicated mathematic operations. It is considered that is even less falsifiable than the manual signature recognition (although this last is already enough trustworthy).
The advantage that Biometrics presents is that the information is unique for each individual and that it can identify the individual in spite of variations in the time (it does not matter if the first biometric sample was taken year ago).The pillars of e-learning security are: authentication, privacy (data confidentiality) authorization (access control), data integrity and non-repudiation. Biometric is a technique that can provide all this requirements with quite lot reliability.
Although biometrics is considered the most effective and safe method (is very difficult to falsify), we have to bear in mind its disadvantages, for example, that since it is a relative new technology, it is not still integrated in PC, so IT departments need to make a conscious decision before making the purchase and change its structure.
We also have to consider the advantages and disadvantages of each individual system. In the next paragraphs, we will make an enumeration of the problems that these techniques can present:
Facial recognition:
Advantages:
a. Non intrusive
b. Cheap technology.
Disadvantages
a. 2D recognition is affected by changes in lighting, the person’s hair, the age, and if the person wear glasses.
b. Requires camera equipment for user identification; thus, it is not likely to become popular until most PCs include cameras as standard equipment.
Voice recognition:
Advantages:
a. Non intrusive. High social acceptability.
b. Verification time is about five seconds.
c. Cheap technology.
Disadvantages:
a. A person’s voice can be easily recorded and used for unauthorised PC or network.
b. Low accuracy.
c. An illness such as a cold can change a person’s voice, making absolute identification difficult or impossible.
Signature recognition:
Advantages:
a. Non intrusive.
b. Little time of verification (about five seconds).
c. Cheap technology.
Disadvantages:
a. Signature verification is designed to verify subjects based on the traits of their unique signature. As a result, individuals who do not sign their names in a consistent manner may have difficulty enrolling and verifying in signature verification.
b. Error rate: 1 in 50.
DNA:
Advantages:
a. Very high accuracy.
b. It impossible that the system made mistakes.
c. It is standardized.
Disadvantages:
a. Extremely intrusive.
b. Very expensive.
Retinal scanning:
Advantages:
a. Very high accuracy.
b. There is no known way to replicate a retina.
c. The eye from a dead person would deteriorate too fast to be useful, so no extra precautions have to been taken with retinal scans to be sure the user is a living human being.
Disadvantages:
a. Very intrusive.
b. It has the stigma of consumer's thinking it is potentially harmful to the eye.
c. Comparisons of template records can take upwards of 10 seconds, depending on the size of the database.
d. Very expensive.
Iris recognition:
Advantages:
a. Very high accuracy.
b. Verification time is generally less than 5 seconds.
c. The eye from a dead person would deteriorate too fast to be useful, so no extra precautions have to been taken with retinal scans to be sure the user is a living human being.
Disadvantages:
a. Intrusive.
b. A lot of memory for the data to be stored.
c. Very expensive
Fingerprint:
Advantages:
a. Very high accuracy.
b. Is the most economical biometric PC user authentication technique.
c. it is one of the most developed biometrics
d. Easy to use.
e. Small storage space required for the biometric template, reducing the size of the database memory required
f. It is standardized.
Disadvantages:
a. For some people it is very intrusive, because is still related to criminal identification.
b. It can make mistakes with the dryness or dirty of the finger’s skin, as well as with the age (is not appropriate with children, because the size of their fingerprint changes quickly).
c. Image captured at 500 dots per inch (dpi). Resolution: 8 bits per pixel. A 500 dpi fingerprint image at 8 bits per pixel demands a large memory space, 240 Kbytes approximately → Compression required (a factor of 10 approximately).
Hand Geometry:
Advantages:
a. Though it requires special hardware to use, it can be easily integrated into other devices or systems.
b. It has no public attitude problems as it is associated most commonly with authorized access.
c. The amount of data required to uniquely identify a user in a system is the smallest by far, allowing it to be used with SmartCards easily.
Disadvantages:
a. Very expensive
b. Considerable size.
c. It is not valid for arthritic person, since they cannot put the hand on the scanner properly.
Comments (0)
You don't have permission to comment on this page.